by Protected_User_16304267 | Aug 12, 2025 | CMMC
The most fundamental question in cybersecurity is: “Who are you?” Before any system can enforce policy, log activity, or prevent unauthorized access, it must first identify the user. That’s what IA.L2-3.5.1 requires: reliable identification of users, processes, and...

by Protected_User_16304267 | May 29, 2024 | Business, Cybersecurity, Documentation
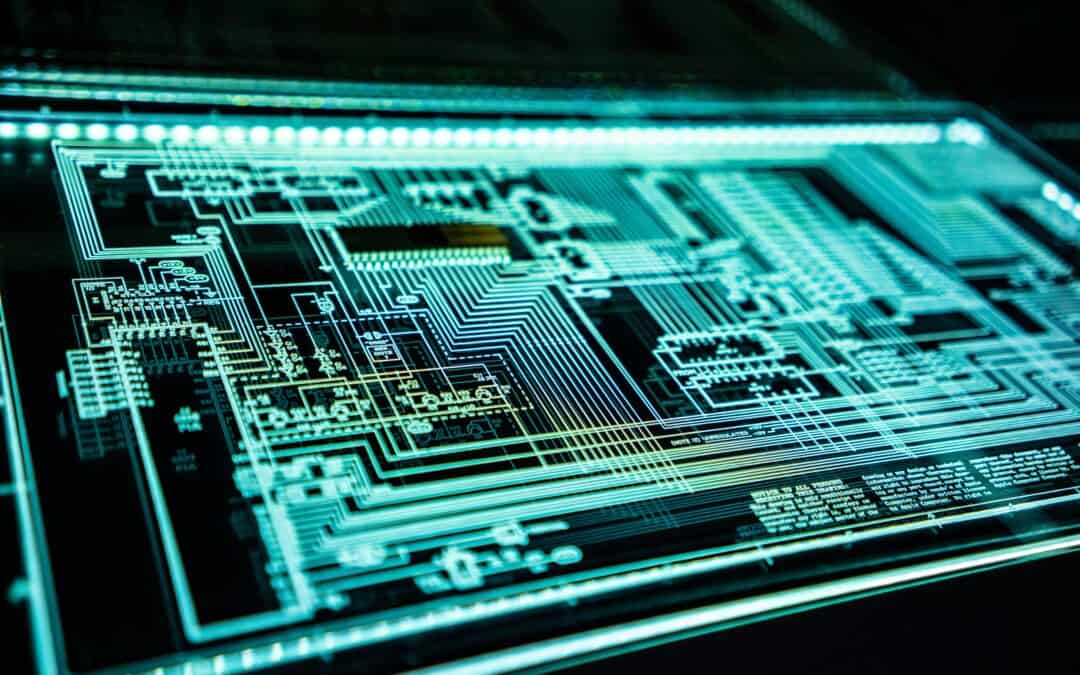
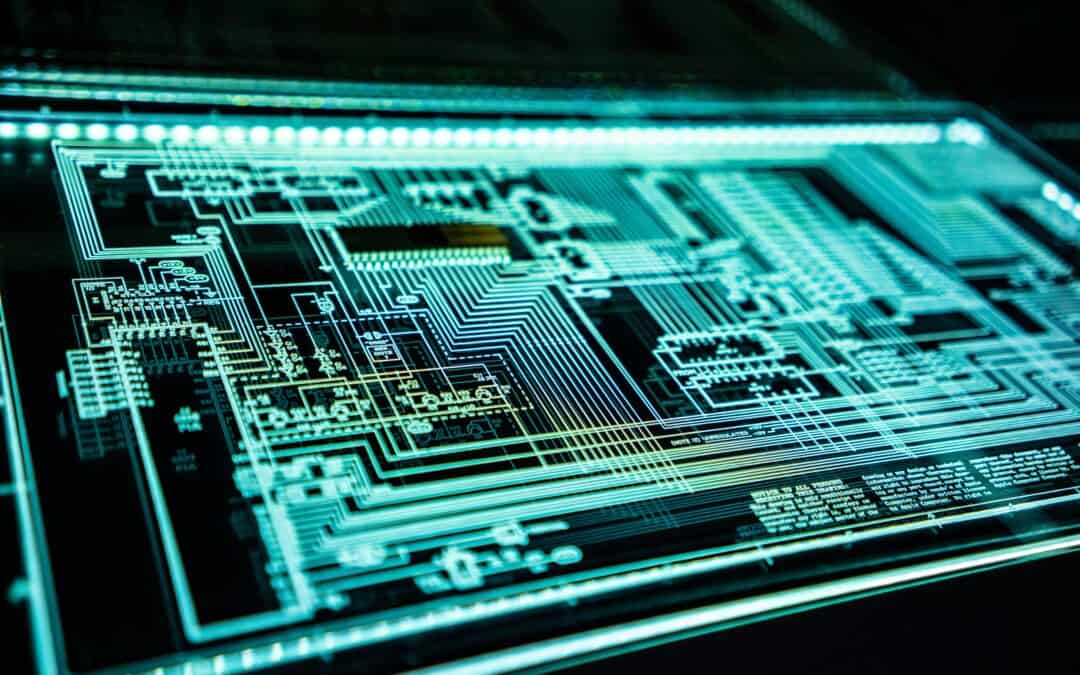
In the fast-evolving landscape of cybersecurity, staying ahead of threats requires more than just cutting-edge technology. It demands a comprehensive strategy that encompasses not only sophisticated tools but also well-defined policies and procedures. One...
by Protected_User_16304267 | May 20, 2024 | Business, Cybersecurity
In today’s world, where cyber trouble seems to be around every corner and data leaks can be a total nightmare, making sure your sensitive info stays safe is crucial, especially for DoD contactors and small businesses. Cyber threats keep changing, so it’s...